Export limit exceeded: 333939 CVEs match your query. Please refine your search to export 10,000 CVEs or fewer.
Export limit exceeded: 333939 CVEs match your query. Please refine your search to export 10,000 CVEs or fewer.
Export limit exceeded: 333939 CVEs match your query. Please refine your search to export 10,000 CVEs or fewer.
Search
Search Results (333939 CVEs found)
| CVE | Vendors | Products | Updated | CVSS v3.1 |
|---|---|---|---|---|
| CVE-2025-4579 | 2025-05-16 | 7.2 High | ||
| The WP Content Security Plugin plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the blocked-uri and effective-directive parameters in all versions up to, and including, 2.3 due to insufficient input sanitization and output escaping. This makes it possible for unauthenticated attackers to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | ||||
| CVE-2025-4564 | 2025-05-16 | 9.8 Critical | ||
| The TicketBAI Facturas para WooCommerce plugin for WordPress is vulnerable to arbitrary file deletion due to insufficient file path validation via the 'delpdf' action in all versions up to, and including, 3.18. This makes it possible for unauthenticated attackers to delete arbitrary files on the server, which can easily lead to remote code execution when the right file is deleted (such as wp-config.php). | ||||
| CVE-2025-32922 | 2025-05-16 | 7.1 High | ||
| Cross-Site Request Forgery (CSRF) vulnerability in Tobias WP2LEADS allows Stored XSS.This issue affects WP2LEADS: from n/a through 3.5.0. | ||||
| CVE-2025-27525 | 2025-05-16 | 3.9 Low | ||
| Information Exposure vulnerability in Hitachi JP1/IT Desktop Management 2 - Smart Device Manager on Windows.This issue affects JP1/IT Desktop Management 2 - Smart Device Manager: from 12-00 before 12-00-08, from 11-10 through 11-10-08, from 11-00 through 11-00-05, from 10-50 through 10-50-06. | ||||
| CVE-2025-27523 | 2025-05-16 | 8.7 High | ||
| XXE vulnerability in Hitachi JP1/IT Desktop Management 2 - Smart Device Manager on Windows.This issue affects JP1/IT Desktop Management 2 - Smart Device Manager: from 12-00 before 12-00-08, from 11-10 through 11-10-08, from 11-00 through 11-00-05, from 10-50 through 10-50-06. | ||||
| CVE-2025-3053 | 2025-05-16 | 8.8 High | ||
| The UiPress lite | Effortless custom dashboards, admin themes and pages plugin for WordPress is vulnerable to Remote Code Execution in all versions up to, and including, 3.5.07 via the uip_process_form_input() function. This is due to the function taking user supplied inputs to execute arbitrary functions with arbitrary data, and does not have any sort of capability check. This makes it possible for authenticated attackers, with Subscriber-level access and above, to execute arbitrary code on the server. | ||||
| CVE-2025-27524 | 2025-05-16 | 5.3 Medium | ||
| Weak encryption vulnerability in Hitachi JP1/IT Desktop Management 2 - Smart Device Manager on Windows.This issue affects JP1/IT Desktop Management 2 - Smart Device Manager: from 12-00 before 12-00-08, from 11-10 through 11-10-08, from 11-00 through 11-00-05, from 10-50 through 10-50-06. | ||||
| CVE-2025-4211 | 2025-05-16 | 7.3 High | ||
| Improper Link Resolution Before File Access ('Link Following') vulnerability in QFileSystemEngine in the Qt corelib module on Windows which potentially allows Symlink Attacks and the use of Malicious Files. Issue originates from CVE-2024-38081. The vulnerability arises from the use of the GetTempPath API, which can be exploited by attackers to manipulate temporary file paths, potentially leading to unauthorized access and privilege escalation. The affected public API in the Qt Framework is QDir::tempPath() and anything that uses it, such as QStandardPaths with TempLocation, QTemporaryDir, and QTemporaryFile.This issue affects all version of Qt up to and including 5.15.18, from 6.0.0 through 6.5.8, from 6.6.0 through 6.8.1. It is fixed in Qt 5.15.19, Qt 6.5.9, Qt 6.8.2, 6.9.0 | ||||
| CVE-2025-47928 | 2025-05-16 | 9.1 Critical | ||
| Spotipy is a Python library for the Spotify Web API. As of commit 4f5759dbfb4506c7b6280572a4db1aabc1ac778d, using `pull_request_target` on `.github/workflows/integration_tests.yml` followed by the checking out the head.sha of a forked PR can be exploited by attackers, since untrusted code can be executed having full access to secrets (from the base repo). By exploiting the vulnerability is possible to exfiltrate `GITHUB_TOKEN` and secrets `SPOTIPY_CLIENT_ID`, `SPOTIPY_CLIENT_SECRET`. In particular `GITHUB_TOKEN` which can be used to completely overtake the repo since the token has content write privileges. The `pull_request_target` in GitHub Actions is a major security concern—especially in public repositories—because it executes untrusted code from a PR, but with the context of the base repository, including access to its secrets. Commit 9dfb7177b8d7bb98a5a6014f8e6436812a47576f reverted the change that caused the issue. | ||||
| CVE-2025-2306 | 2025-05-16 | 5.9 Medium | ||
| An Improper Access Control vulnerability was identified in the file download functionality. This vulnerability allows users to download sensitive documents without authentication, if the URL is known. The attack requires the attacker to know the documents UUIDv4. | ||||
| CVE-2025-2305 | 2025-05-16 | 8.6 High | ||
| A Path traversal vulnerability in the file download functionality was identified. This vulnerability allows unauthenticated users to download arbitrary files, in the context of the application server, from the Linux server. | ||||
| CVE-2025-40629 | 2025-05-16 | N/A | ||
| PNETLab 4.2.10 does not properly sanitize user inputs in its file access mechanisms. This allows attackers to perform directory traversal by manipulating file paths in HTTP requests. Specifically, the application is vulnerable to requests that access sensitive files outside the intended directory. | ||||
| CVE-2024-26152 | 1 Humansignal | 1 Label Studio | 2025-05-16 | 4.7 Medium |
| ### Summary On all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability. ### Details Need permission to use the "data import" function. This was reproduced on Label Studio 1.10.1. ### PoC 1. Create a project.  2. Upload a file containing the payload using the "Upload Files" function.   The following are the contents of the files used in the PoC ``` { "data": { "prompt": "labelstudio universe image", "images": [ { "value": "id123#0", "style": "margin: 5px", "html": "<img width='400' src='https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif' onload=alert(document.cookie)>" } ] } } ``` 3. Select the text-to-image generation labeling template of Ranking and scoring   4. Select a task 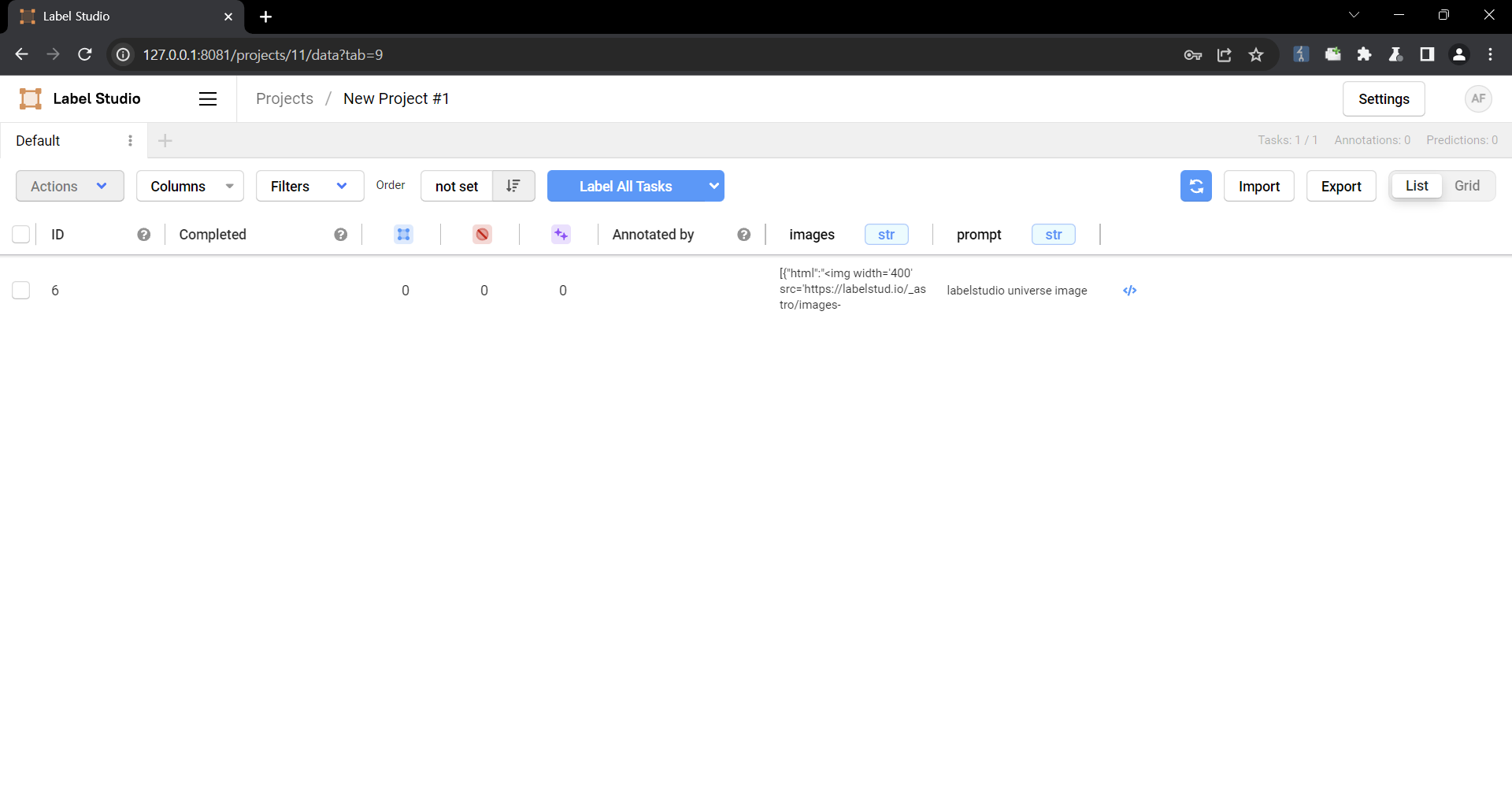 5. Check that the script is running 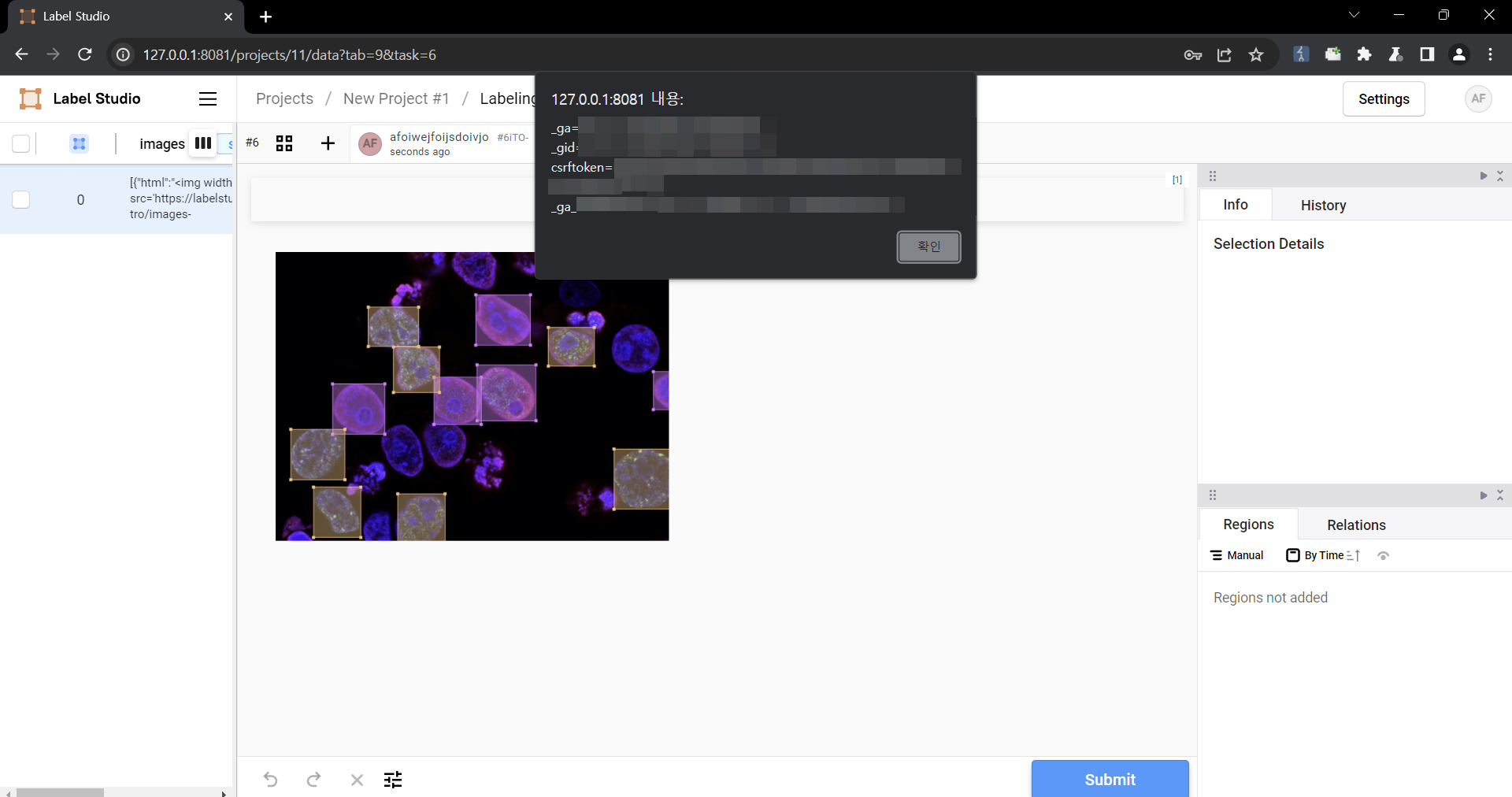 ### Impact Malicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering. | ||||
| CVE-2023-3966 | 3 Fedoraproject, Openvswitch, Redhat | 4 Fedora, Openvswitch, Enterprise Linux and 1 more | 2025-05-16 | 7.5 High |
| A flaw was found in Open vSwitch where multiple versions are vulnerable to crafted Geneve packets, which may result in a denial of service and invalid memory accesses. Triggering this issue requires that hardware offloading via the netlink path is enabled. | ||||
| CVE-2025-4500 | 1 Code-projects | 1 Hotel Management System | 2025-05-16 | 5.3 Medium |
| A vulnerability, which was classified as critical, has been found in code-projects Hotel Management System 1.0. Affected by this issue is the function Edit of the component Edit Room. The manipulation of the argument roomnumber leads to stack-based buffer overflow. An attack has to be approached locally. The exploit has been disclosed to the public and may be used. | ||||
| CVE-2022-42160 | 1 Dlink | 6 Covr 1200, Covr 1200 Firmware, Covr 1202 and 3 more | 2025-05-16 | 8.8 High |
| D-Link COVR 1200,1202,1203 v1.08 was discovered to contain a command injection vulnerability via the system_time_timezone parameter at function SetNTPServerSettings. | ||||
| CVE-2022-42159 | 1 Dlink | 6 Covr 1200, Covr 1200 Firmware, Covr 1202 and 3 more | 2025-05-16 | 4.3 Medium |
| D-Link COVR 1200,1202,1203 v1.08 was discovered to have a predictable seed in a Pseudo-Random Number Generator. | ||||
| CVE-2022-34021 | 1 Resiot | 1 Iot Platform And Lorawan Network Server | 2025-05-16 | 5.4 Medium |
| Multiple Cross Site Scripting (XSS) vulnerabilities in ResIOT IOT Platform + LoRaWAN Network Server through 4.1.1000114 via the form fields. | ||||
| CVE-2022-34020 | 1 Resiot | 1 Iot Platform And Lorawan Network Server | 2025-05-16 | 8.8 High |
| Cross Site Request Forgery (CSRF) vulnerability in ResIOT ResIOT IOT Platform + LoRaWAN Network Server through 4.1.1000114 allows attackers to add new admin users to the platform or other unspecified impacts. | ||||
| CVE-2022-33106 | 1 Wijungle | 2 U250, U250 Firmware | 2025-05-16 | 9.8 Critical |
| WiJungle NGFW Version U250 was discovered to be vulnerable to No Rate Limit attack, allowing the attacker to brute force the admin password leading to Account Take Over. | ||||
